#CyberWeekly
Olympic cyberwars: Russia targets Milano Cortina with 120+ DDoS attacks
The Winter Olympics got a cyberattack before the first medal was awarded. Pro-Russian hacktivist group NoName057(16) launched over 120 DDoS attacks targeting Italy's Milano Cortina 2026 Winter Games — hitting hotel websites in Cortina, government portals including the Foreign Ministry, and Italian consulates in Sydney, Toronto, and Paris. The group framed it as retaliation for Italy's support of Ukraine.
What makes this interesting:
- Scale of response: Italy launched its first-ever round-the-clock cybersecurity command center in Rome, monitoring all venues and coordinating defenses — the most extensive cyber operation ever mounted for a sporting event
- Hotel targeting: NoName057(16) specifically went after hospitality infrastructure where athletes are staying — a reminder that supply chain targets extend far beyond IT systems
- No significant disruption: Italy's ACN (National Cybersecurity Agency) successfully thwarted the attacks. Preparation beats panic
- Pattern recognition: This group has previously hit France (La Poste, Dec 2025), Poland, Czechia, and Lithuania — any European country supporting Ukraine is a target
The lesson for SMEs: You don't need to be an Olympic venue to get caught in geopolitical crossfire. DDoS preparedness and basic resilience planning matter for every business — because hacktivists don't check your revenue before they attack.
Platform Spotlight: Your compliance GPS has arrived

Imagine opening the app and knowing exactly what to do next — every single time. This week we shipped the guided compliance Navigator, a todo-driven workflow that turns audit readiness from a vague aspiration into a concrete, step-by-step journey.
- Assess your CyFun level automatically — enter your sector and company size, get your required controls. One click to apply
- Follow a guided plan — the Navigator shows your next step with a [Go] button. Complete it, and it advances based on what you actually did
- Todo-driven compliance — each todo links to the wiki page where the real work happens. Fill in a policy? Evidence auto-completes. Writing IS compliance
- Live compliance score — dashboards show completion, evidence gaps by NIST function, and prioritized action items. No spreadsheets
For MSPs: Onboard a new client and have them on a guided compliance path within minutes. The Navigator does the project management — you focus on the security expertise.
Odido breach: 6.2 million Dutch customers exposed by a phone call
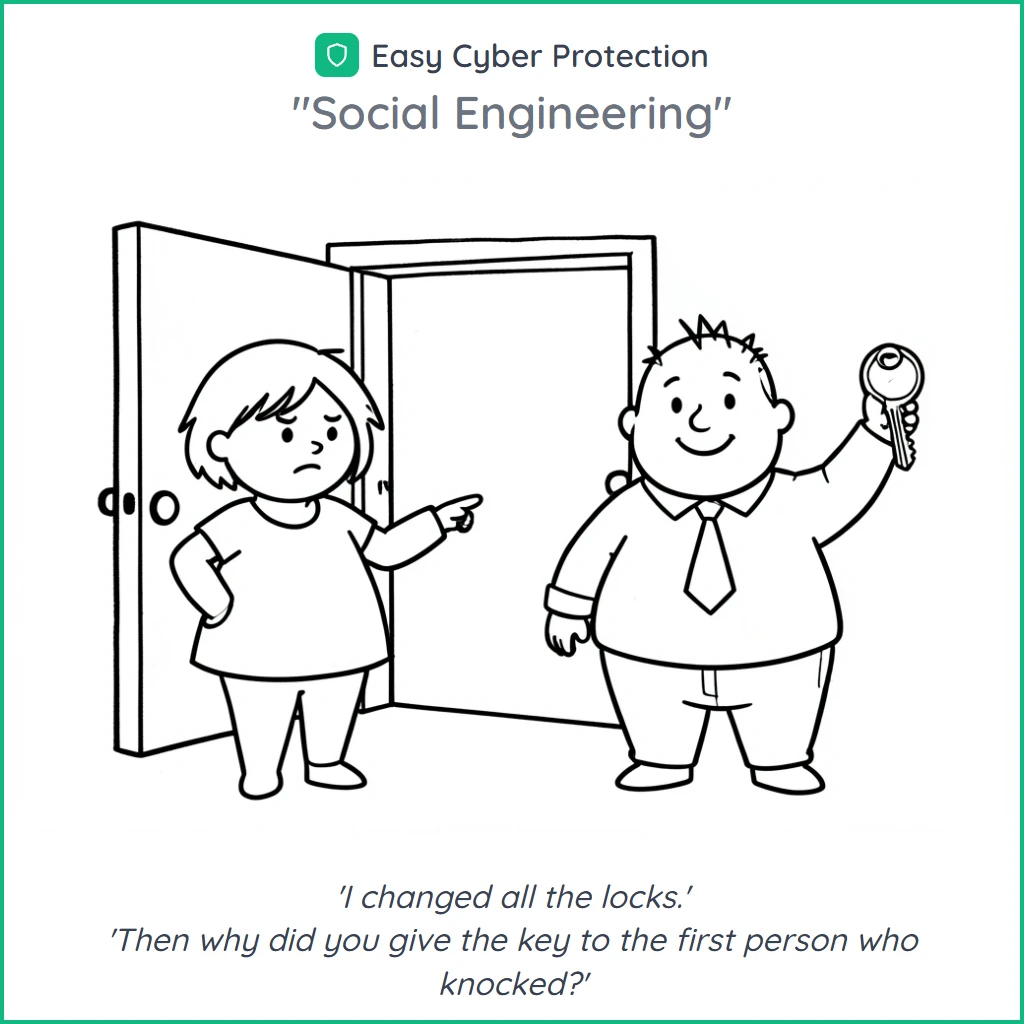
The Netherlands' largest mobile operator just lost 6.2 million customer records — and the attackers didn't exploit a single vulnerability. Dutch telecom giant Odido confirmed on February 13 that criminals used social engineering to bypass multi-factor authentication, calling employees while pretending to be the IT department. Classic, devastating, and entirely preventable.
What was stolen:
- Names, home addresses, email addresses, phone numbers
- Dates of birth and bank account numbers
- ID document details (though not scans of the documents themselves)
- Passwords, call records, and location data were not accessed
Why this matters for Belgian businesses: Odido serves the Dutch market, but cross-border data flows mean Belgian customers of Dutch services could be affected. More importantly, this is a textbook social engineering attack — no zero-day required, just a convincing phone call. If your employee security training doesn't cover voice phishing (vishing), this is your wake-up call. Literally.
BeyondTrust scores a near-perfect 9.9 — on the CVSS vulnerability scale

When your remote access tool scores 9.9 out of 10 on the vulnerability scale, "critical" doesn't quite capture it. CVE-2026-1731, a command injection flaw in BeyondTrust Remote Support and Privileged Remote Access, is actively being exploited in the wild — with proof-of-concept code circulating since February 10.
The ugly details:
- CVSS 9.9 (v4.0) / 9.8 (v3.1) — about as bad as vulnerabilities get
- Unauthenticated WebSocket endpoint — attackers don't need credentials to exploit it
- Remote code execution via unsafe Bash arithmetic evaluation in the
thin-scc-wrapperscript - Affected: Remote Support ≤25.3.1 and Privileged Remote Access ≤24.3.4
- Fixed in: RS 25.3.2+ and PRA 25.1.1+ — patch immediately
MSPs, this one's personal. BeyondTrust is widely used for remote support and privileged access management — exactly the tools MSPs rely on to manage client environments. If you or your clients use BeyondTrust, verify your version today. GreyNoise, watchTowr, and Arctic Wolf all confirm active exploitation. For broader context on keeping your tools updated, review your patch management process.
Belgium's NIS2 milestone: 2,410 organizations registered — and counting
Belgium just pulled off the largest cybersecurity compliance operation in its history. The Centre for Cybersecurity Belgium (CCB) announced that 2,410 organizations from critical sectors have registered under NIS2 — with a total of over 4,000 registrations across all sectors. Given that roughly 2,500 organizations are estimated to be in scope, that's a near-complete registration rate.
What this means:
- Registration is done — self-assessment is next. The April 18 deadline for CyFun self-assessment submission is now 8 weeks away. Registered doesn't mean compliant
- Energy, transport, healthcare, digital infrastructure, government, and manufacturing — these sectors make up the 2,410 critical registrations
- The CCB's CyFun framework is the mandatory assessment tool. Organizations must submit a CyFun self-assessment or equivalent (ISO 27001) to the CCB
- MSP opportunity: Thousands of organizations now need help preparing their self-assessment in 8 weeks. That's a lot of compliance work that needs doing
If you haven't started your NIS2 compliance checklist yet, the clock is ticking. Registration was the easy part. The self-assessment requires actual evidence of security controls in place — policies documented, procedures tested, inventories maintained. That's exactly what a structured compliance roadmap is for.